Comparison Shortlist
Machine-Ready Briefs: AI turns undefined needs into a technical project request.
We use cookies to improve your experience and analyze site traffic. You can accept all cookies or only essential ones.
Stop browsing static lists. Tell Bilarna your specific needs. Our AI translates your words into a structured, machine-ready request and instantly routes it to verified Retail Security Solutions experts for accurate quotes.
Machine-Ready Briefs: AI turns undefined needs into a technical project request.
Verified Trust Scores: Compare providers using our 57-point AI safety check.
Direct Access: Skip cold outreach. Request quotes and book demos directly in chat.
Precision Matching: Filter matches by specific constraints, budget, and integrations.
Risk Elimination: Validated capacity signals reduce evaluation drag & risk.
Ranked by AI Trust Score & Capability
Run a free AEO + signal audit for your domain.
AI Answer Engine Optimization (AEO)
List once. Convert intent from live AI conversations without heavy integration.
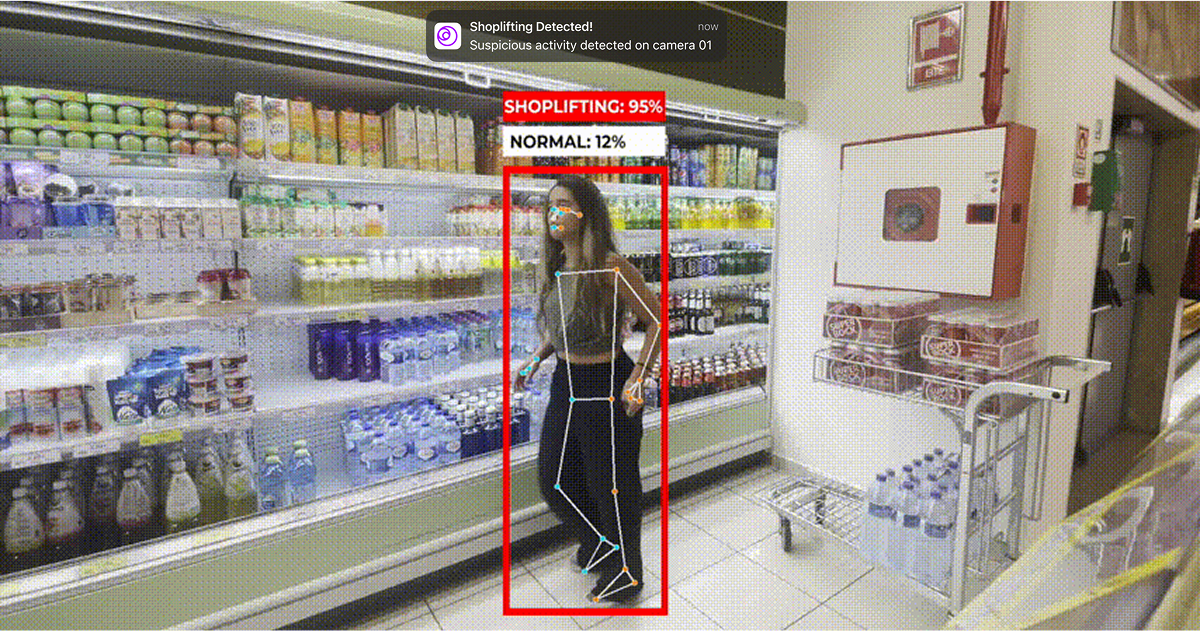
Retail security solutions are integrated systems designed to prevent theft, reduce shrinkage, and enhance safety in physical retail environments. These solutions leverage technologies such as AI-powered video analytics, electronic article surveillance (EAS), access control, and real-time monitoring to detect suspicious behavior, deter shoplifting, and secure high-value merchandise. They serve industries including supermarkets, department stores, specialty retailers, and convenience stores. Core benefits include significant loss prevention, improved operational efficiency, enhanced customer and employee safety, and data-driven insights into store activity.
Providers of retail security solutions include specialized security technology vendors, video surveillance companies, and integrated systems integrators. These firms often hold certifications in physical security, cybersecurity for connected devices, and compliance with data privacy regulations like GDPR. Many develop proprietary AI algorithms for behavior analytics and object recognition. The market includes global security giants offering comprehensive suites, as well as agile startups focusing on cloud-native, AI-driven theft prevention software that integrates with existing camera infrastructure.
Retail security solutions work by integrating hardware like cameras and sensors with software platforms that analyze video feeds in real-time using computer vision. A typical workflow involves site assessment, installation of equipment, system configuration, and staff training on responding to alerts. Common pricing models include monthly SaaS subscriptions based on the number of cameras or store square footage, upfront capital expenditure for hardware, and hybrid models. Implementation can take from a few days for software-only solutions to several weeks for full hardware rollouts. Providers typically offer online quoting tools, digital proposal uploads, and post-deployment feedback channels for continuous optimization.
Shoplifting detection – systems to prevent retail theft. Discover and compare verified providers using the AI Trust Score on Bilarna.
View Shoplifting Detection providersYes, modern paywall solutions are designed to be compatible with both iOS and Android mobile applications. This cross-platform compatibility ensures that developers can implement a single paywall system across different devices and operating systems without needing separate solutions. It simplifies management and provides a consistent user experience regardless of the platform, making it easier to maintain and optimize monetization strategies.
Yes, plant-based meat products are suitable for both restaurants and retail stores. They offer a clean-label, versatile protein option that can appeal to a wide range of customers, including those seeking vegan or plant-based alternatives. Restaurants can incorporate these products into their menus to provide innovative dishes such as plant-based steaks, ribs, or fish filets, catering to diverse dietary preferences. Retail stores can stock these items to meet growing consumer demand for sustainable and ethical food choices. Offering plant-based meats can help businesses attract new customers and support environmentally friendly practices while providing delicious and satisfying meal options.
Yes, AI video analytics solutions are designed to integrate seamlessly with existing security systems without the need for hardware modifications. This means organizations can enhance their video surveillance capabilities by adding AI-driven analytics without replacing cameras, servers, or other infrastructure components. The software typically connects to current video feeds and security platforms, allowing users to apply customized rules, attach images for improved detection, and receive detailed reports. This flexibility reduces implementation costs and downtime, enabling businesses to upgrade their security operations efficiently while maintaining their current hardware investments.
Yes, financial automation solutions are often modular and customizable to fit the specific needs of different businesses. Organizations can select and adapt only the modules they require, such as accounts payable, accounts receivable, billing, or treasury management, allowing them to scale their automation at their own pace. This flexibility ensures that companies can address their unique operational challenges without unnecessary complexity or cost. Additionally, user-friendly tools and AI capabilities enable teams to maintain compliance and efficiency while tailoring the system to their workflows. Customized onboarding and collaborative support further help businesses get up and running quickly with solutions that match their requirements.
Nanotechnology-based coating solutions are developed by designing materials and processes at the nanoscale with a clear target application in mind. This involves iterative cycles of testing and optimization to enhance performance and functionality. By focusing on the intended use from the start, developers can tailor the coatings to meet specific requirements such as durability, conductivity, or protective properties. The vertical integration of the development process ensures that each stage, from nanoscale design to final application, is aligned to achieve the best possible outcome.
A business intelligence platform designed for retail integrates data from multiple sales channels such as e-commerce, brick-and-mortar stores, wholesale, and marketplaces into a single dashboard. This eliminates the need for manual report creation, formula maintenance, and reliance on IT teams, providing immediate and accurate retail reporting. Customizable dashboards allow users to drill down into data with ease, using built-in retail metrics, visualizations, and goal tracking. Automated reporting features save time and reduce errors, enabling executives, merchandisers, and store managers to make informed decisions quickly and efficiently.
A business intelligence platform designed for retail can consolidate data from various sales channels such as e-commerce, brick-and-mortar stores, wholesale, and marketplaces into a single dashboard. This integration eliminates the need for manual report generation, reduces errors caused by formula maintenance, and removes dependency on IT teams. Retailers gain immediate access to accurate, real-time data, enabling faster decision-making and better inventory management. Customizable dashboards with built-in retail metrics and visualizations allow users to drill down into data effortlessly, improving overall operational efficiency and sales performance.
Improve SaaS application security by deploying a cloud access security broker (CASB) that provides comprehensive visibility and control. Steps: 1. Integrate CASB via API or inline deployment to continuously monitor SaaS applications. 2. Identify and remediate misconfigurations, exposed files, and suspicious activities. 3. Apply zero trust policies to regulate user and device access. 4. Enforce granular data loss prevention controls to block risky data sharing. 5. Ensure compliance with regulations like GDPR, CCPA, and HIPAA through enhanced visibility and control.
A company can implement AI solutions for all employees by adopting an enterprise-ready platform that offers both user-friendly AI chat assistants and developer tools for custom workflows. This approach ensures that non-technical staff can benefit from AI-powered assistants tailored to specific use cases, while developers have the flexibility to build, automate, and deploy custom AI applications. Key features include model-agnostic support, data privacy compliance, integration capabilities with existing tools, and scalable deployment options. Providing educational resources and seamless integration with communication platforms helps facilitate adoption across the organization.
Line-based protocols process input line by line, which can introduce security vulnerabilities if the protocol does not properly validate or restrict commands. In networked developer tools that accept commands over TCP connections, ignoring unknown commands or not enforcing strict authentication can allow attackers to inject malicious commands. For example, if a server accepts an EVAL command on its own line without verifying the source or content, an attacker can craft requests that exploit this behavior. Additionally, because HTTP is also a line-based protocol, attackers can disguise malicious commands within HTTP requests, bypassing normal protocol expectations. This can lead to unauthorized code execution and compromise of the system running the developer tool.