Machine-Ready Briefs
AI translates unstructured needs into a technical, machine-ready project request.
We use cookies to improve your experience and analyze site traffic. You can accept all cookies or only essential ones.
Stop browsing static lists. Tell Bilarna your specific needs. Our AI translates your words into a structured, machine-ready request and instantly routes it to verified Cloud Security Solutions experts for accurate quotes.
AI translates unstructured needs into a technical, machine-ready project request.
Compare providers using verified AI Trust Scores & structured capability data.
Skip the cold outreach. Request quotes, book demos, and negotiate directly in chat.
Filter results by specific constraints, budget limits, and integration requirements.
Eliminate risk with our 57-point AI safety check on every provider.
Verified companies you can talk to directly

a true Managed Server Specialist since 1996.

Expert managed IT services in San Francisco - proactive support, cloud & security solutions for growing businesses.

Tresal provides comprehensive attack surface management and cloud security solutions. Discover vulnerabilities, secure your assets, and protect your business. Start your free trial today.
Learn how Cloudflare's cloud access security broker (CASB) improves security across your SaaS applications with less overhead. Deploy in-line or via API.
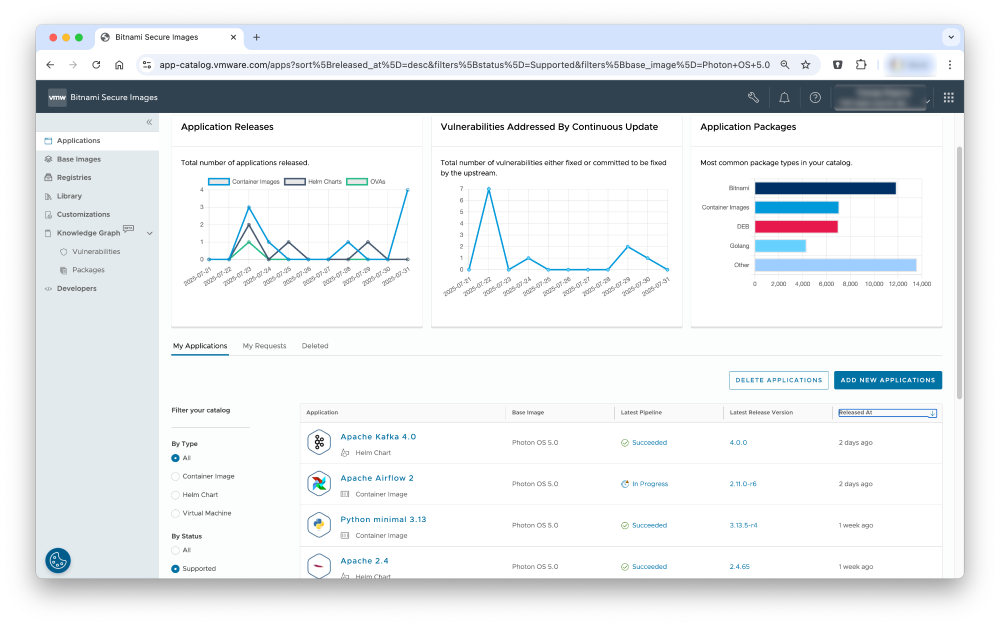
Confidence, control and visibility of your software supply chain security with production-ready open source software delivered continuously in hardened images
Run a free AEO + signal audit for your domain.
AI Answer Engine Optimization (AEO)
List once. Convert intent from live AI conversations without heavy integration.
Cloud security solutions are a set of policies, controls, and technologies designed to protect cloud-based data, applications, and infrastructure. They typically involve tools for identity and access management, data encryption, threat detection, and compliance monitoring. Implementing these solutions mitigates risks like data breaches and ensures business continuity by securing digital assets across public, private, or hybrid cloud deployments.
An initial assessment identifies vulnerabilities, compliance gaps, and misconfigurations within the existing cloud infrastructure to establish a security baseline.
Specialized tools and policies are implemented to secure data, manage access, and monitor network traffic for potential threats across the cloud environment.
Ongoing automated monitoring, threat intelligence, and incident response protocols actively defend against evolving cyber threats in real-time.
Securing transaction data and customer PII to meet stringent regulations like PCI-DSS and GDPR while preventing sophisticated fraud and attacks.
Protecting electronic health records (EHR) and research data to ensure HIPAA compliance and safeguard sensitive patient information from breaches.
Shielding customer payment data and personally identifiable information during transactions to maintain trust and prevent costly data theft.
Embedding security into the application architecture to protect multi-tenant customer data and ensure service availability and integrity.
Securing connected industrial systems and IoT device data from operational technology (OT) threats that could disrupt production or cause safety issues.
Bilarna evaluates every cloud security solutions provider through a rigorous 57-point AI Trust Score. This proprietary system analyzes expertise, technical certifications, client delivery track records, and compliance with standards like ISO 27001 and SOC 2. Bilarna's continuous monitoring ensures providers maintain high reliability and performance standards, giving buyers confidence in their selection.
Core features include identity and access management (IAM), data encryption both in transit and at rest, continuous security monitoring (CSM), and automated compliance checks. A robust solution also offers threat intelligence, vulnerability management, and detailed logging for forensic analysis to provide comprehensive protection.
Costs vary widely based on cloud environment size, required features, and deployment model, often ranging from tens to hundreds of thousands annually. Pricing models include per-user subscriptions, consumption-based fees, or flat-rate enterprise licenses, with significant factors being the level of support and customization needed.
Traditional security focuses on protecting a defined network perimeter, while cloud security adopts a data-centric, zero-trust model for dynamic, scalable environments. Cloud solutions are API-driven, designed for shared responsibility models, and protect assets across geographically dispersed infrastructure not owned by the organization.
A full implementation typically takes 3 to 6 months, depending on the complexity of the existing cloud footprint and the scope of security controls. The process involves assessment, planning, phased tool deployment, configuration, policy definition, and staff training to ensure proper adoption and operation.
Common pitfalls include choosing a provider without expertise in your specific cloud platform (e.g., AWS vs. Azure) and overlooking the need for 24/7 managed detection and response (MDR). Failing to verify compliance certifications and real-world client references for similar deployments also leads to inadequate protection and support.
Yes, modern paywall solutions are designed to be compatible with both iOS and Android mobile applications. This cross-platform compatibility ensures that developers can implement a single paywall system across different devices and operating systems without needing separate solutions. It simplifies management and provides a consistent user experience regardless of the platform, making it easier to maintain and optimize monetization strategies.
Yes, AI video analytics solutions are designed to integrate seamlessly with existing security systems without the need for hardware modifications. This means organizations can enhance their video surveillance capabilities by adding AI-driven analytics without replacing cameras, servers, or other infrastructure components. The software typically connects to current video feeds and security platforms, allowing users to apply customized rules, attach images for improved detection, and receive detailed reports. This flexibility reduces implementation costs and downtime, enabling businesses to upgrade their security operations efficiently while maintaining their current hardware investments.
Yes, financial automation solutions are often modular and customizable to fit the specific needs of different businesses. Organizations can select and adapt only the modules they require, such as accounts payable, accounts receivable, billing, or treasury management, allowing them to scale their automation at their own pace. This flexibility ensures that companies can address their unique operational challenges without unnecessary complexity or cost. Additionally, user-friendly tools and AI capabilities enable teams to maintain compliance and efficiency while tailoring the system to their workflows. Customized onboarding and collaborative support further help businesses get up and running quickly with solutions that match their requirements.
Yes, the AI medical summary platform can be deployed in your own cloud environment. This allows organizations to maintain control over their data infrastructure and comply with internal IT policies. Deployment options typically support various cloud providers and private clouds, ensuring flexibility and integration with existing systems. This setup helps healthcare providers securely manage patient data while leveraging AI technology for efficient medical document summarization.
Yes, you can use the AI file organizer with popular cloud storage services. Follow these steps: 1. Install the AI file organization app on your device. 2. Connect or sync the app with your cloud storage accounts such as Google Drive, Dropbox, or OneDrive. 3. Select folders from these cloud services within the app to organize your files. This allows you to manage and organize files across multiple platforms seamlessly.
Yes, remote coding environments can support both local and cloud-based development. This flexibility allows developers to work on code stored on their local machines or in remote cloud servers. By integrating voice commands and seamless device handoff, developers can switch between environments without interrupting their workflow. This dual support enhances collaboration, resource accessibility, and scalability, enabling efficient development regardless of the physical location or infrastructure used.
Nanotechnology-based coating solutions are developed by designing materials and processes at the nanoscale with a clear target application in mind. This involves iterative cycles of testing and optimization to enhance performance and functionality. By focusing on the intended use from the start, developers can tailor the coatings to meet specific requirements such as durability, conductivity, or protective properties. The vertical integration of the development process ensures that each stage, from nanoscale design to final application, is aligned to achieve the best possible outcome.
Smart contracts are used in enterprise blockchain solutions to automate complex business processes, enforce agreements without intermediaries, and significantly reduce operational costs and manual errors. These self-executing contracts are deployed on blockchain platforms to manage and execute terms automatically when predefined conditions are met. Common enterprise applications include automating supply chain payments upon delivery verification, managing and executing royalty distributions in intellectual property agreements, and facilitating secure, instant settlement in trade finance. They are also foundational for creating decentralized autonomous organizations (DAOs), tokenizing real-world assets like real estate or carbon credits, and building transparent, tamper-proof voting systems for corporate governance. By leveraging smart contracts, enterprises can achieve greater transparency, enhance auditability, and streamline workflows across departments and with external partners.
Choosing between on-premise and cloud-based communications solutions depends on evaluating specific business factors including upfront capital expenditure, scalability needs, maintenance resources, and security requirements. On-premise systems involve higher initial hardware and software licensing costs but offer direct control over data and infrastructure, potentially appealing to organizations with strict data residency regulations or existing robust IT teams for maintenance. Cloud-based solutions, like Hosted VoIP, typically operate on a predictable subscription model with lower upfront costs, automatic updates, and inherent scalability, allowing businesses to add or remove users and features easily as needs change. Key decision criteria include total cost of ownership over 3-5 years, required uptime and reliability, integration capabilities with existing business applications, the need for remote or mobile workforce support, and internal technical expertise to manage the system. Most modern businesses favor cloud solutions for their flexibility, reduced IT burden, and continuous access to the latest features.
A business can improve its website security through a multi-layered approach focusing on server security, application security, and third-party services. First, robust server security is foundational and involves using secure hosting providers, implementing firewalls, and keeping server software and operating systems updated with the latest security patches. Second, website security itself requires measures like enforcing HTTPS with SSL/TLS certificates, using strong password policies and multi-factor authentication for admin access, regularly updating the content management system and all plugins, and conducting frequent security audits and vulnerability scans. Third, securing third-party services is critical; this includes vetting and monitoring any integrated APIs, widgets, or external scripts for security compliance and ensuring payment gateways and analytics tools are configured securely. Regular backups, a Web Application Firewall, and a clear incident response plan complete a comprehensive security posture.