Comparison Shortlist
Machine-Ready Briefs: AI turns undefined needs into a technical project request.
We use cookies to improve your experience and analyze site traffic. You can accept all cookies or only essential ones.
Stop browsing static lists. Tell Bilarna your specific needs. Our AI translates your words into a structured, machine-ready request and instantly routes it to verified Cybersecurity Compliance experts for accurate quotes.
Machine-Ready Briefs: AI turns undefined needs into a technical project request.
Verified Trust Scores: Compare providers using our 57-point AI safety check.
Direct Access: Skip cold outreach. Request quotes and book demos directly in chat.
Precision Matching: Filter matches by specific constraints, budget, and integrations.
Risk Elimination: Validated capacity signals reduce evaluation drag & risk.
Ranked by AI Trust Score & Capability


Run a free AEO + signal audit for your domain.
AI Answer Engine Optimization (AEO)
List once. Convert intent from live AI conversations without heavy integration.
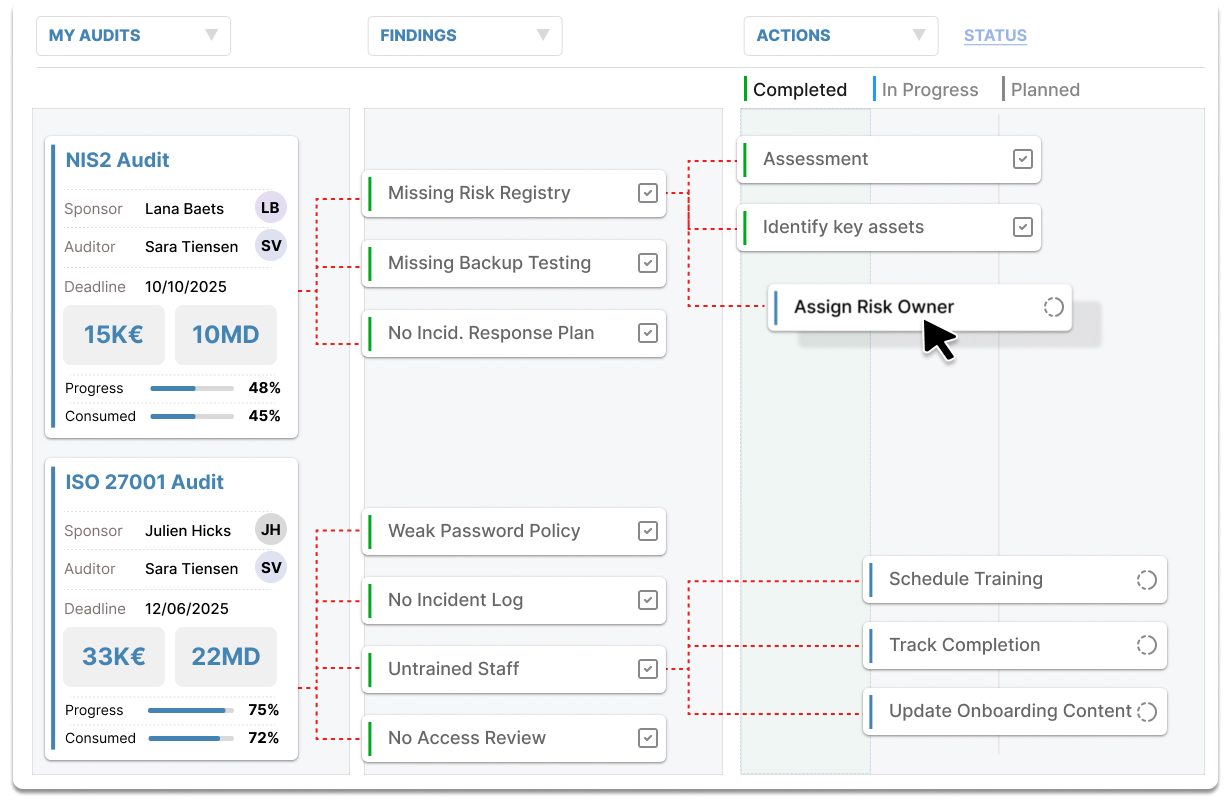
Cybersecurity compliance services help organizations meet regulatory standards such as NIS2, ISO 27001, and GDPR. These services include audits, remediation, and continuous monitoring to ensure data protection and security. They address the need for businesses to demonstrate compliance, reduce cybersecurity risks, and avoid penalties. By implementing these solutions, companies can enhance their security posture, protect sensitive information, and build trust with clients and partners. The services are tailored for small to medium-sized enterprises seeking quick and effective compliance setup, often within a few days.
Cybersecurity compliance services are provided by specialized cybersecurity firms, consulting agencies, and IT service providers. These organizations have expertise in security standards, risk management, and regulatory requirements. They work closely with businesses to assess their current security posture, identify gaps, and implement tailored solutions. Many providers offer quick deployment options, ensuring compliance setup within a few days. Their goal is to help organizations meet legal obligations, improve security defenses, and build trust with stakeholders.
Delivery of cybersecurity compliance services typically involves initial assessments, tailored remediation plans, and rapid deployment to meet regulatory deadlines. Pricing varies based on the scope and complexity of the organization’s needs, with many providers offering flexible packages. Setup often includes system audits, vulnerability assessments, and implementation of security controls. Some services are offered as ongoing support or managed solutions, ensuring continuous compliance and security. Customers benefit from expert guidance, transparent pricing, and quick turnaround times, often within a few days.
Automated compliance and privacy analysis uses AI to monitor regulatory adherence. Compare and select verified solution providers on the Bilarna platform.
View Compliance & Privacy Analysis providersCybersecurity compliance assessment — a structured audit of your IT security against regulations. Find and compare verified providers with objective 57-point AI Trust Scores on Bilarna.
View Cybersecurity Compliance Assessment providersCybersecurity compliance services help businesses meet regulatory standards and secure data. Compare trusted, AI-vetted providers on Bilarna's B2B marketplace.
View Cybersecurity Compliance Services providersAI compliance platforms are designed to complement, not replace, customs brokers in the import process. These platforms provide automated audits and classification recommendations to identify errors and potential savings, but they do not file customs entries, corrections, or paperwork with customs authorities. Licensed customs brokers remain essential for submitting filings and handling official communications. The AI platform offers defensible evidence and insights that brokers can use to improve accuracy and compliance, enhancing the overall import process without substituting the broker's role.
A compliance and learning management platform centralizes the organization and maintenance of internal policies and procedures in a structured hub. It allows assigning owners to specific documents, tracking different versions, setting review cycles, and routing approvals through built-in workflow compliance tools. This ensures that all policies are up to date and properly managed, reducing the risk of non-compliance and making it easier for teams to access and follow internal guidelines.
A compliance management platform streamlines the certification process by providing expert guidance and handling much of the heavy lifting involved. It offers tailored support that adapts to your business needs, helping you stay organized and focused on critical tasks. Such platforms often include features like step-by-step instructions, direct communication channels, and open-source tools that reduce vendor lock-in. This approach simplifies complex compliance requirements, reduces wasted time and costs, and ensures you are audit-ready efficiently. By partnering with a knowledgeable platform, organizations can navigate certifications like SOC 2, GDPR, HIPAA, and ISO more smoothly and with greater confidence.
A compliance partner can significantly ease the SOC 2 certification process for startups by providing expert guidance and hands-on support throughout the journey. Startups often face confusion, wasted time, and high costs when managing multiple systems independently. A dedicated partner helps clarify complex requirements, explains and implements necessary controls, and keeps the process organized and on track. They anticipate the startup's needs, reduce administrative burdens by handling heavy lifting tasks, and offer tailored solutions that fit the company's size and workflow. Additionally, a good compliance partner can assist with vendor security assessments and enterprise contract requirements, ensuring startups meet all necessary standards efficiently and with less stress.
Implement cybersecurity software that proactively detects and blocks phishing attacks. 1. Deploy software that monitors user endpoints for suspicious emails and links. 2. Enable real-time alerts to notify users of potential phishing attempts. 3. Use detection algorithms to identify malicious attachments and fraudulent communications. 4. Intercept attacks before users click on harmful links. 5. Continuously update threat databases to recognize new phishing tactics.
A digital asset management platform can streamline tax withholding and compliance by integrating with HRIS systems to automate net-of-withholding token distributions. It supports tracking and managing tax deductions for various grant types, including restricted token units (RTUs). The platform offers custom reporting capabilities to meet specific tax and compliance requirements. By automating these processes, it reduces manual errors and administrative burden, ensuring that token distributions comply with relevant tax laws. Additionally, expert support is often available to help navigate complex legal frameworks and maintain alignment between on-chain and off-chain agreements.
A fiduciary company helps clients navigate complex tax laws by ensuring accurate tax filings and identifying opportunities for tax optimization. They analyze financial situations to recommend strategies that minimize tax liabilities while complying with legal requirements. This includes preparing tax returns, advising on deductible expenses, and planning for future tax obligations. By staying updated on changes in tax legislation, fiduciary companies provide proactive advice to help clients avoid penalties and maximize tax efficiency.
A global HR and payroll system designed for the MENA region helps businesses manage compliance by integrating local labor laws, payroll regulations, and leave policies into a single platform. This ensures that companies remain compliant with country-specific requirements such as wage protection systems, social insurance, and pension contributions across multiple countries like UAE, Saudi Arabia, Egypt, and others. The system automates compliance tasks, reduces manual errors, and provides a unified source of truth for workforce data, enabling seamless management of employees and contractors across borders while minimizing legal risks and administrative burdens.
A unified platform that combines identity verification, fraud protection, and compliance simplifies the process of expanding a business globally. It allows companies to verify both businesses and individuals across multiple countries efficiently, reducing the risk of fraud and ensuring adherence to regulatory requirements. By integrating various local identity vendors through one API, businesses can customize onboarding flows and apply risk-based decisioning to prevent fraudulent activities while maintaining a smooth customer experience. This approach streamlines compliance management, enables quick decision-making via a centralized dashboard, and supports audit trail monitoring and report generation, ultimately accelerating global growth without added complexity.
A software development partner ensures compliance for a healthcare project by first possessing certified expertise in relevant healthcare data standards and regulations, such as HIPAA in the US, GDPR for EU data, and HL7 for clinical data interchange. The process involves conducting a thorough compliance audit at the project's outset to map all data flows, identify protected health information (PHI), and define access controls. Development is then guided by privacy-by-design and security-by-design principles, incorporating features like end-to-end encryption, strict user authentication, detailed audit trails, and robust data anonymization techniques. The partner must also establish formal data processing agreements, ensure all third-party components are compliant, and facilitate regular security assessments and penetration testing. Ultimately, their role is to architect a system that not only meets functional requirements but also embeds regulatory adherence into its core infrastructure.