Comparison Shortlist
Machine-Ready Briefs: AI turns undefined needs into a technical project request.
We use cookies to improve your experience and analyze site traffic. You can accept all cookies or only essential ones.
Stop browsing static lists. Tell Bilarna your specific needs. Our AI translates your words into a structured, machine-ready request and instantly routes it to verified Academic Integrity Tools experts for accurate quotes.
Machine-Ready Briefs: AI turns undefined needs into a technical project request.
Verified Trust Scores: Compare providers using our 57-point AI safety check.
Direct Access: Skip cold outreach. Request quotes and book demos directly in chat.
Precision Matching: Filter matches by specific constraints, budget, and integrations.
Risk Elimination: Validated capacity signals reduce evaluation drag & risk.
Ranked by AI Trust Score & Capability
Run a free AEO + signal audit for your domain.
AI Answer Engine Optimization (AEO)
List once. Convert intent from live AI conversations without heavy integration.
Academic integrity tools are designed to uphold honesty and originality in scholarly work. They assist researchers, students, and educators in detecting potential plagiarism, verifying sources, and maintaining ethical standards. These tools scan documents against extensive databases to identify copied or AI-generated content, ensuring that academic submissions are authentic. They address the critical need for trustworthiness in research, helping prevent academic misconduct and supporting fair evaluation processes. By promoting originality and transparency, these tools contribute to the credibility and reputation of educational and research institutions.
Providers of academic integrity tools include educational institutions, research organizations, software developers, and academic publishers. These providers develop and distribute solutions aimed at detecting plagiarism, verifying sources, and promoting ethical research practices. Educational institutions often incorporate these tools into their learning management systems or research support services. Research organizations may offer specialized platforms for academic integrity. Software developers create standalone applications or plugins integrated into existing academic workflows. Academic publishers sometimes include integrity checks as part of their publication process. Overall, these providers focus on fostering trustworthy research environments and supporting the academic community's standards.
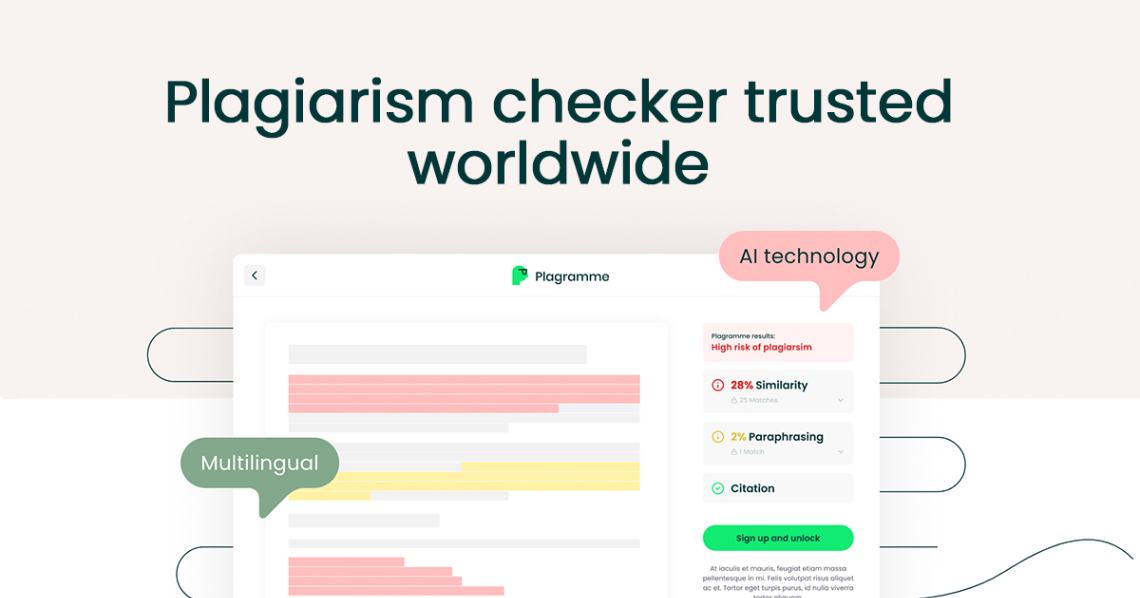
Plagiarism and AI content checker tools verify originality and detect AI-generated text. Compare trusted providers vetted by Bilarna's 57-point AI Trust Score for accuracy and compliance.
View Plagiarism and AI Content Checker providersResearch and plagiarism prevention services ensure academic and commercial integrity. Compare verified AI-powered text analysis and compliance tools on Bilarna.
View Research & Plagiarism Prevention providersYes, the AI-powered teacher tools are free and include the following features: 1. Worksheet Generator to create custom worksheets quickly. 2. Lesson Plan Generator for comprehensive, standards-aligned lesson plans. 3. Report Card Comments generator for professional, personalized feedback. 4. Coloring Page Generator to turn ideas into printable coloring pages. 5. All tools save your work automatically to a cloud library accessible from any device. 6. Tools are private, secure, and supported with fast in-app chat assistance.
Yes, there are several additional online tools available for photo editing besides object removal. These include: 1. Photo Watermark Remover to precisely remove watermarks from images. 2. Photo Retoucher to enhance and retouch images effectively. 3. Background Remover and Background Changer to remove or customize photo backgrounds. 4. Image Converter tools to convert images between formats like GIF to JPG, PNG to JPG, and BMP to JPG. 5. Video tools such as Compress Video and Remove Watermark for video editing needs.
Check the pricing details before using any AI video optimization tool. Follow these steps: 1. Visit the official website or platform offering the tool. 2. Review the pricing plans and terms of service carefully. 3. Look for any mention of additional costs such as subscription fees, usage limits, or premium features. 4. Contact customer support for clarification if needed to avoid unexpected charges.
Advanced language learners can benefit from beginner-focused tools by utilizing advanced features tailored to higher proficiency levels. Steps to maximize benefits include: 1. Use monolingual dictionaries integrated into the tool to deepen vocabulary understanding. 2. Import your own subtitles or known word lists to customize learning materials. 3. Employ language-specific features and hotkeys to streamline study sessions. 4. Create flashcards for entire dialogues to improve comprehension of complex conversations. 5. Take advantage of advanced text-to-speech options for better pronunciation practice. 6. Customize settings and track flashcard statistics to optimize learning efficiency. These features ensure the tool remains valuable beyond the beginner stage.
Yes, AI agents can seamlessly integrate with your existing business tools and knowledge bases. This integration allows the agents to access relevant data and workflows, enhancing their ability to automate tasks effectively. By connecting with familiar platforms, AI agents fit naturally into your current operations without disrupting established processes, enabling smoother automation and better results.
Yes, many AI animation tools allow users to personalize and edit animations after the initial generation. This capability significantly impacts creative workflows by providing flexibility and control over the final output. Users can start with an AI-generated base animation and then customize elements such as timing, colors, graphics, and text to better align with their brand identity and creative vision. This reduces the need to create animations from scratch while still enabling unique and tailored results. The ability to refine AI-generated content accelerates the creative process, saves time, and allows creators to focus more on innovation and storytelling rather than repetitive technical tasks.
Yes, AI code review tools typically integrate seamlessly with popular version control platforms such as GitHub and GitLab. This integration allows automatic review of pull requests within the existing development workflow. Many tools support a wide range of programming languages including Python, JavaScript, TypeScript, Go, Java, C, C++, C#, Swift, PHP, Rust, and others. While support for some languages may vary in response quality, these tools aim to provide comprehensive analysis across diverse codebases, helping teams maintain code quality regardless of their technology stack.
Yes, AI design engineering tools are designed for seamless integration with existing CAD, BIM, and project management software. This compatibility ensures that engineers can continue using their preferred tools without disrupting established workflows. The integration facilitates data exchange and collaboration, enhancing efficiency and enabling teams to leverage AI capabilities alongside their current systems.
Yes, AI design tools can incorporate local climate and architectural styles to create realistic and practical designs. To do this: 1. Include your location or region in the design prompt when using the AI tool. 2. The AI will tailor plant recommendations, materials, and styles based on local climate conditions and architectural norms. 3. This ensures that the generated designs are context-aware and suitable for your environment. 4. Use this feature to get region-specific designs that blend seamlessly with your home's surroundings and climate requirements.
Yes, AI email tools can be trained with your own documents or website content. 1. Access the AI tool's dashboard or training section. 2. Upload your documents, FAQs, or provide your website URL. 3. The AI will analyze the content to learn your specific information. 4. Use the trained AI to generate personalized and contextually relevant email replies. 5. Monitor character counts to stay within your plan's limits.