Machine-Ready Briefs
AI translates unstructured needs into a technical, machine-ready project request.
We use cookies to improve your experience and analyze site traffic. You can accept all cookies or only essential ones.
Stop browsing static lists. Tell Bilarna your specific needs. Our AI translates your words into a structured, machine-ready request and instantly routes it to verified Secure Data Management experts for accurate quotes.
AI translates unstructured needs into a technical, machine-ready project request.
Compare providers using verified AI Trust Scores & structured capability data.
Skip the cold outreach. Request quotes, book demos, and negotiate directly in chat.
Filter results by specific constraints, budget limits, and integration requirements.
Eliminate risk with our 57-point AI safety check on every provider.
Verified companies you can talk to directly
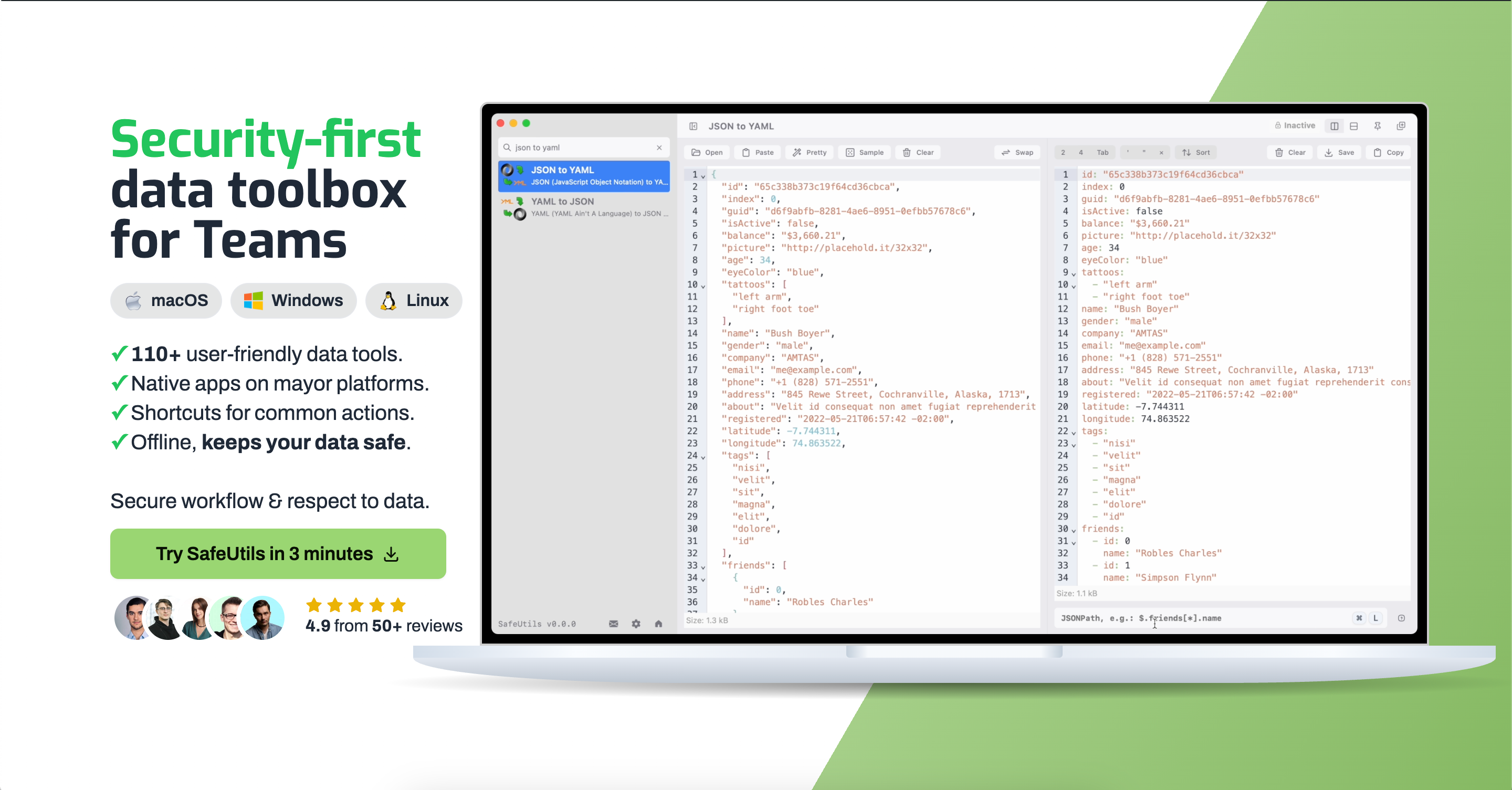
Native macOS, Linux and Windows desktop application with 110+ carefully crafted tools for yours and your teams everyday work with sensitive data in all formats.

Tower is a secure AI-powered VDR that lawyers and M&A teams use to build deal-ready data rooms and run diligence in minutes.
Your AI Assistant for Design Engineering. Free your engineers to focus on high-value work.

Speck records your meetings, automates your research workflows, and performs actions on your behalf so you can spend more time on what matters.
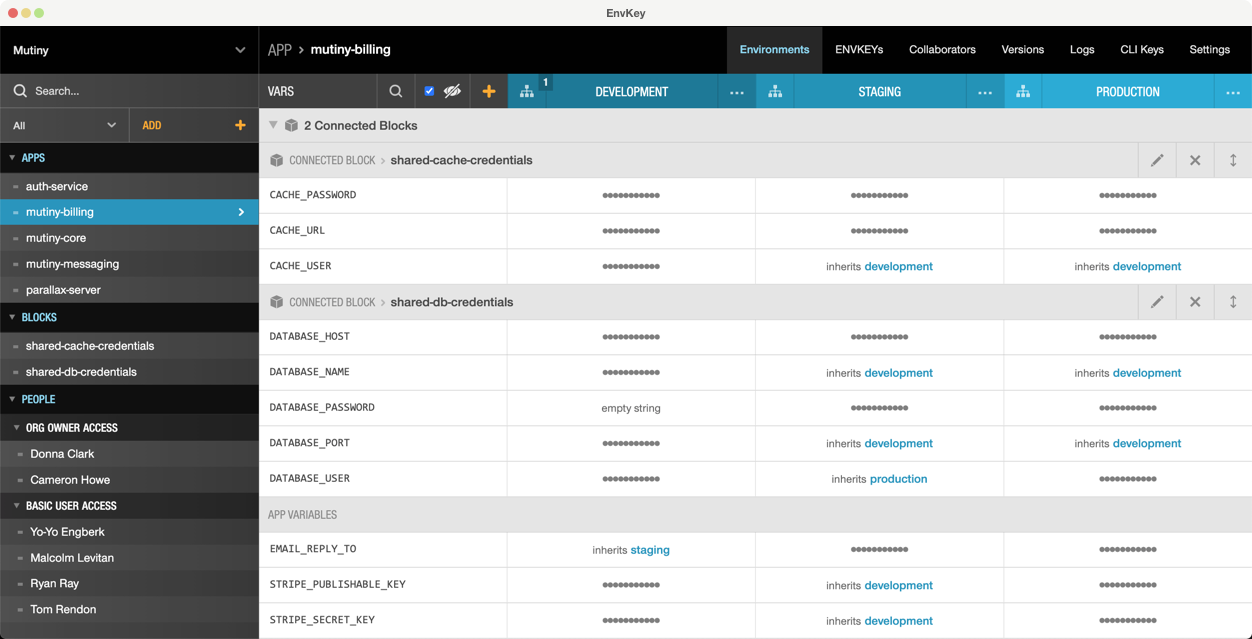
Protect API keys and other secrets with end-to-end encryption. Keep configuration organized and in sync.
Agentic AI introduces a new kind of risk: autonomous digital actors operating with privilege beyond traditional controls. Anjuna becomes the incorruptible supervisor, isolating agents in TEEs, enforcing policy at runtime, and preventing unauthorized actions or data exposure.
Automate your on-call with data-aware AI agents
Run a free AEO + signal audit for your domain.
AI Answer Engine Optimization (AEO)
List once. Convert intent from live AI conversations without heavy integration.
Secure Data Management is the integrated strategy and technical controls for protecting, governing, and controlling enterprise data throughout its entire lifecycle. It combines technologies like encryption, access controls, and data masking to ensure confidentiality, integrity, and availability. For businesses, it minimizes risk, ensures compliance with regulations like GDPR, and safeguards valuable digital assets.
Sensitive data is identified, categorized, and its potential security threats are assessed to define protection requirements.
Technical and organizational measures like encryption, access management, and activity logging are established and enforced.
The security posture is continuously monitored, audits are conducted, and controls are adapted to new threats and compliance demands.
Protects highly sensitive financial data and transactions, meets stringent regulatory mandates like PSD2, and enables secure open banking.
Secures patient health information under privacy laws, enables secure telemedicine services, and facilitates compliant research data pools.
Safeguards customer and payment data from breaches, builds consumer trust, and ensures PCI DSS compliance for online transactions.
Secures massive production and IoT sensor data from tampering, protects intellectual property and ensures operational integrity.
Enables multi-tenant, compliant data residency for cloud software, ensures data sovereignty, and manages cross-border data flows securely.
Bilarna evaluates Secure Data Management providers using a proprietary 57-point AI Trust Score measuring expertise, reliability, compliance, and client satisfaction. Verification includes portfolio reviews, reference checks, validation of certifications (e.g., ISO 27001, SOC 2), and continuous service quality monitoring. This ensures decision-makers connect only with qualified and trustworthy partners.
Costs vary significantly based on scope, data volume, and compliance needs. Typical models include software licensing, implementation services, and ongoing maintenance fees. A detailed requirements analysis is essential for an accurate quote.
Implementation typically ranges from 3 to 12 months. Duration depends on IT landscape complexity, required data migration, and integration with legacy systems. Structured project planning is critical for success.
Data security focuses on protection from unauthorized access and threats. Secure data management is a holistic framework integrating security into the entire data lifecycle, including governance, quality, and compliance.
Key regulations include GDPR, industry-specific rules like HIPAA in healthcare, or PCI DSS for payment data. Robust data management helps centrally demonstrate and meet these requirements.
Common pitfalls are focusing solely on price, ignoring scalability needs, and insufficient due diligence on the provider's compliance expertise. A strategic vendor evaluation is crucial for long-term value.
Yes, AI voice and SMS agents designed for healthcare are built with security and compliance in mind. They adhere to industry standards and regulations such as HIPAA (Health Insurance Portability and Accountability Act) to protect patient data privacy and security. Business Associate Agreements (BAAs) are available to formalize compliance commitments. Additionally, these agents comply with regulations like TCPA (Telephone Consumer Protection Act) and PCI (Payment Card Industry) standards where applicable. Ensuring security and regulatory compliance is critical to maintaining trust and safeguarding sensitive healthcare information while leveraging AI technologies.
Yes, conversations with AI companions are private and secure. To ensure confidentiality, platforms use advanced encryption and data protection measures. Steps to maintain privacy include: 1. Encrypting chat data during transmission and storage. 2. Implementing strict access controls to prevent unauthorized access. 3. Regularly updating security protocols to address vulnerabilities. 4. Providing users with privacy policies detailing data handling. Always verify the platform's security features before use.
Conversations with an AI girlfriend are generally designed to be private and secure, with platforms implementing encryption and data protection measures to safeguard user information. However, privacy policies vary between services, so it is important to review the specific app or platform’s privacy policy to understand how your data is handled. Users are advised to avoid sharing sensitive personal information during chats, as AI systems are not substitutes for secure human interactions. While many platforms strive to maintain confidentiality, exercising caution and understanding the terms of service is essential for protecting your privacy.
Yes, online therapy sessions are designed to be fully confidential and secure. Reputable platforms follow strict privacy protocols and data security measures to protect your personal information. All communications during therapy sessions are encrypted, ensuring that what you share remains private. Additionally, therapists adhere to professional confidentiality standards similar to those in face-to-face therapy. This means your information is safeguarded under professional secrecy laws, providing a safe environment for emotional support and healing.
To understand data upload limits and payment requirements on analytics platforms, follow these steps: 1. Review the platform's account types, such as free and paid plans. 2. Check the data upload limits for each plan; free accounts often have row limits per upload. 3. Determine if a credit card is required for free or paid accounts. 4. Understand the cancellation policy for paid subscriptions, which usually allows cancellation at any time.
Typically, after an initial trial period—often around seven days—business management software platforms do not charge monthly fees or enforce minimum usage requirements. Instead, continued use is contingent upon subscribing to a paid plan. This approach allows users to evaluate the software's features risk-free before committing financially. It is advisable to review the specific pricing details and terms on the provider's official website to understand any conditions related to payment plans, as these can vary between services.
Virtual cards provide a secure way to spend money online or in-store without needing a physical card. They can be created instantly in any currency and location, offering enhanced security by reducing the risk of card theft or fraud. Users can set spending limits on each virtual card, monitor transactions easily, and manage multiple cards from one platform. This makes virtual cards an ideal solution for both individuals and businesses looking for flexible, safe payment options.
Yes, a Laboratory Information Management System is designed to integrate seamlessly with various software systems and devices. This integration capability allows automatic transfer of test results and other data between the LIMS and external applications, reducing manual data entry and minimizing errors. It supports connectivity with laboratory instruments, billing systems, and other business software, enabling a unified workflow. Users can access test results and invoices from any device, ensuring flexibility and convenience. Such integrations enhance data accuracy, improve operational efficiency, and facilitate better communication across different platforms used within the laboratory environment.
Yes, AI dental receptionists can integrate seamlessly with most major practice management systems (PMS) that offer online appointment pages or APIs. This integration allows the AI to book appointments directly into your existing system, pull customer form responses from your CRM, and route calls to the correct clinic and calendar. Such integration ensures that all patient interactions are synchronized with your practice’s workflow, improving efficiency and reducing manual data entry errors.
Yes, AI design engineering tools are designed for seamless integration with existing CAD, BIM, and project management software. This compatibility ensures that engineers can continue using their preferred tools without disrupting established workflows. The integration facilitates data exchange and collaboration, enhancing efficiency and enabling teams to leverage AI capabilities alongside their current systems.