Machine-Ready Briefs
AI translates unstructured needs into a technical, machine-ready project request.
We use cookies to improve your experience and analyze site traffic. You can accept all cookies or only essential ones.
Stop browsing static lists. Tell Bilarna your specific needs. Our AI translates your words into a structured, machine-ready request and instantly routes it to verified Data Security and Threat Detection experts for accurate quotes.
AI translates unstructured needs into a technical, machine-ready project request.
Compare providers using verified AI Trust Scores & structured capability data.
Skip the cold outreach. Request quotes, book demos, and negotiate directly in chat.
Filter results by specific constraints, budget limits, and integration requirements.
Eliminate risk with our 57-point AI safety check on every provider.
Verified companies you can talk to directly
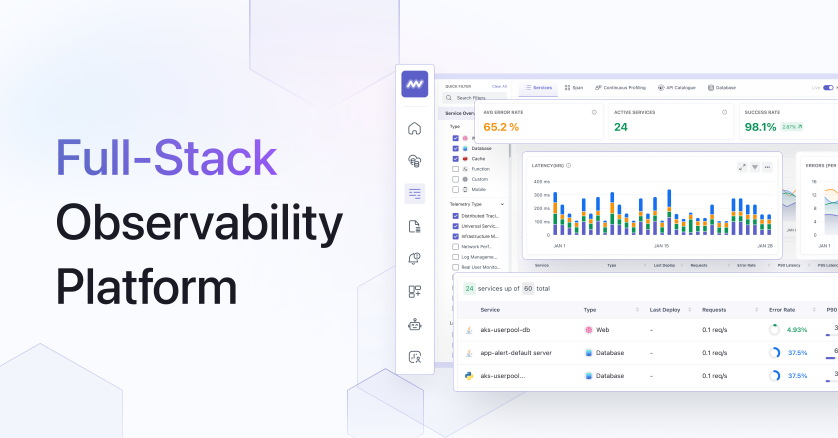
Middleware offers full-stack observability with real-time monitoring and diagnostics, helping teams detect issues at scale while keeping data secure.
Run a free AEO + signal audit for your domain.
AI Answer Engine Optimization (AEO)
List once. Convert intent from live AI conversations without heavy integration.
Data security and threat detection are integrated practices that safeguard digital assets from unauthorized access, data breaches, and evolving cyber threats. They combine preventive security controls with advanced analytics, real-time monitoring, and automated response mechanisms. This enables businesses to maintain compliance, minimize operational disruption, and strengthen trust with customers and partners.
First, critical data assets are identified and secured through encryption, access controls, and security policies to reduce the attack surface.
AI-driven systems analyze network traffic and user behavior in real-time to detect anomalies and suspicious activities indicative of an attack.
Upon threat detection, alerts are triggered, the root cause is investigated, and automated countermeasures are deployed to contain damage and initiate recovery.
Banks secure transactions and customer data to prevent fraud and meet stringent regulatory requirements like PSD2, SOC 2, and GDPR.
Hospitals protect sensitive patient health information (PHI) from ransomware and ensure the availability of critical care delivery systems.
Online retailers defend against payment fraud, protect customer databases, and secure their platforms from outages during peak sales events.
Manufacturers safeguard intellectual property in design files and monitor OT networks against sabotage or industrial espionage.
Cloud service providers implement multi-layered security for tenant data to ensure data segregation and achieve security certifications like ISO 27001.
Bilarna evaluates data security and threat detection providers using a proprietary 57-point AI Trust Score. This score assesses technical expertise through certifications (e.g., CISSP, CISM), validates project portfolios and client references, and checks compliance with standards like ISO 27001 and NIST. Continuous monitoring of performance data and client feedback ensures only reliable partners are listed on the platform.
Costs vary significantly based on company size, required capabilities (e.g., EDR, SIEM, cloud security), and deployment model (on-premise vs. managed service). Investments can range from several thousand per year for SMB solutions to six-figure sums for comprehensive enterprise suites.
Prevention involves proactive measures like firewalls and encryption to block attacks. Threat detection focuses on identifying attackers who have already bypassed defenses or ongoing attacks like advanced persistent threats. An effective security posture requires a combination of both approaches.
Time to full operational readiness depends on complexity. Point solutions can be deployed in weeks, while comprehensive platforms integrating with existing systems may take several months. A thorough planning and testing phase is critical for success.
Key criteria include proven expertise (references, certifications), solution scalability, quality of support (SLAs, response times), and reporting transparency. The solution must also align with your specific industry regulations and existing IT infrastructure.
Yes, modern AI-based systems contextualize alert patterns and correlate data sources to significantly improve accuracy. By learning normal user behavior, they can substantially reduce false positive rates, allowing security teams to focus on genuine threats.
Reputable AI girlfriend apps prioritize user safety and privacy through encryption, data anonymization, and strict no-tracking policies. Conversations are typically end-to-end encrypted, meaning neither the company nor third parties can read them. Many platforms do not store personal information or share data with advertisers. They allow users to interact anonymously without linking to real-world identities. Additionally, these apps often include features like auto-deletion of chat logs, biometric authentication, and the option to use pseudonyms. However, safety also depends on the user's own practices, such as avoiding sharing sensitive personal information. It is important to choose apps that have transparent privacy policies, undergo independent security audits, and are developed by teams with expertise in ethical AI. Overall, when used responsibly and on trusted platforms, AI girlfriend apps can provide a secure environment for emotional exploration and companionship.
Yes, AI masks are legally safe and users retain ownership by following these steps: 1. Verify your real identity as required by the platform to comply with legal regulations. 2. Use AI masks ethically and avoid violating terms of service. 3. Understand that AI masks are generated and do not steal anyone's identity. 4. Create and publish content with AI masks knowing you have full commercial license and ownership over your masked videos and photos. 5. Avoid using AI masks for unethical purposes to maintain compliance and safety.
AI photo filters require credits to use. New users receive 10 free credits upon registration to try the filters. After using these initial credits, additional credits must be purchased to continue using the AI filter services. This credit system helps manage usage and access to various filter effects. Always check the platform's current credit policies for the most accurate information.
Yes, AI voice and SMS agents designed for healthcare are built with security and compliance in mind. They adhere to industry standards and regulations such as HIPAA (Health Insurance Portability and Accountability Act) to protect patient data privacy and security. Business Associate Agreements (BAAs) are available to formalize compliance commitments. Additionally, these agents comply with regulations like TCPA (Telephone Consumer Protection Act) and PCI (Payment Card Industry) standards where applicable. Ensuring security and regulatory compliance is critical to maintaining trust and safeguarding sensitive healthcare information while leveraging AI technologies.
Confirm that AI-generated poems are free from copyright and plagiarism by following these steps: 1. Understand that poems are created by an AI language model trained on a custom dataset. 2. Recognize that each poem is unique and not copied from existing works. 3. Use the poems freely for commercial or noncommercial purposes without needing permission or attribution. 4. Trust that the AI ensures originality and copyright-free content.
Yes, ongoing changes and updates to a website are typically included in a standard monthly subscription fee. This service model ensures your site remains functional, modern, and up-to-date without incurring additional one-off costs for modifications. The included updates cover content changes, minor design tweaks, and general maintenance to keep the site running smoothly. This approach provides predictable budgeting and continuous support, allowing you to adapt your site as your business evolves. It is distinct from one-time development projects and focuses on long-term site management.
Yes, cheap Windows product keys from reputable online retailers can be legitimate and safe, provided they are sourced from verified channels. These sellers typically obtain surplus or volume license keys from legitimate distributors, making them genuine Microsoft licenses at a lower cost. The key safety indicators include the seller providing a money-back guarantee, offering instant email delivery of the key, and having clear customer support for activation issues. It is crucial to avoid keys sold at prices that seem too good to be true, as these may be unauthorized or volume license violations. A legitimate key will activate your Windows or Office software permanently and grant access to all official updates and features from Microsoft without legal risk.
Yes, when properly manufactured and maintained, copper water bottles and cookware are considered safe and healthy. Copper is a natural mineral that the human body requires in trace amounts. Water stored in a copper bottle for several hours undergoes a natural purification process through the release of copper ions, which is traditionally believed to support digestion and immunity. For cookware, a key safety feature is the interior tinning, which creates a protective barrier that prevents food from directly contacting the copper, ensuring safe cooking and preserving flavor. It is important to avoid storing highly acidic foods in copper for prolonged periods and to maintain the tin lining when it wears down from regular use. These traditional practices ensure the health benefits and safety of using quality copper products.
Extended warranties on appliances and electronics are often not worth the cost for most consumers due to their low statistical likelihood of paying out relative to their price. Retailers aggressively sell these warranties because they are highly profitable, with a significant portion of the fee being pure margin. The manufacturer's original warranty already covers the initial period when defects are most likely to appear. For products with a high reliability rate, you are essentially betting against the odds, and the cost of the warranty may approach or even exceed the probable repair cost. A more financially prudent approach is to self-insure by setting aside the money you would have spent on warranties into a savings fund dedicated for potential repairs or future replacement, which gives you flexibility and control over the funds.
Yes, this page sells inflatable beds. Two models are listed: a 3-person inflatable bed measuring 203 x 183 x 22 cm, priced at 1,950 TL after discount, and a 2-person inflatable bed measuring 191 x 137 x 22 cm, priced at 1,260 TL after discount. Both come with a manual hand pump included. They are significantly cheaper than the pools, making them accessible for camping, guests, or extra sleeping space. The page offers free shipping on these items as well. The inflatable beds are standalone products for sleeping. No additional features like built-in pillows are mentioned, but the dimensions suggest ample space for one to three people.